Why this matters
Security sees an alert. Observability holds the truth about impact.
In real deployments, Security and Observability often live in separate serverless projects and clusters. That separation is healthy for ownership—but it becomes a liability when analysts must guess whether an incident is noisy or business-critical.
The pattern
Agent Builder: let each domain keep its expertise
Build a Security agent and an Observability agent in separate Serverless projects, then wire Kibana Workflows so an alert can POST to the other project’s /api/agent_builder/converse before a Case is created.
- Bidirectional lab — Security alerts can ask Observability; Observability alerts can ask Security (same HTTP pattern, swapped URL + agent id).
- No duplicated analytics — each agent keeps domain tools; workflow calls stay API-first across projects.
- One case narrative — drill copy plus the peer agent reply (or a captured HTTP error if the call fails).
Reference workflow
Two data planes, one place to decide
Security telemetry (endpoint, EDR, firewalls) and Observability signals (APM, infrastructure, application logs) both land in Elastic—where rules, workflows, cases, and dashboards give analysts a single narrative. Linked Agent Builder agents add cross-project reasoning when those streams live in separate serverless projects.
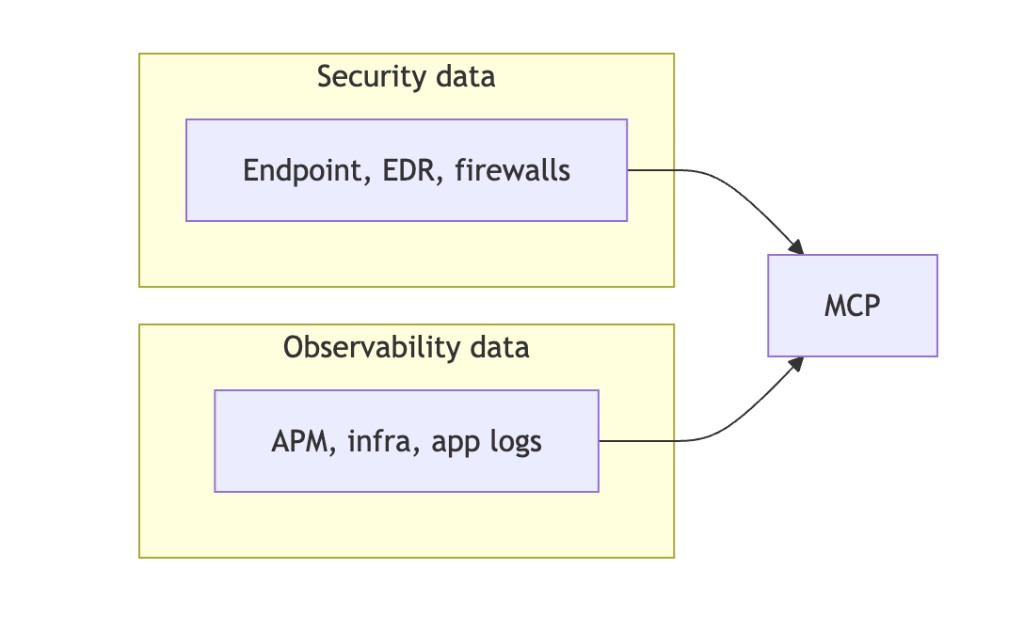
- Left lanes — keep collection specialized; avoid duplicating analytics in both stacks.
- MCP / Agent Builder — detections, triage, workflow automation, and the enriched case document analysts ship.
- Cross-project call (A2A) — Workflows use native HTTP to the peer Kibana converse endpoint (Basic or API key). Kibana’s outbound connector is still capped near ~60s, so the lab uses a short [A2A_WF] path on the Observability agent for Security-initiated peer review.
- Cross-project search (CPS) — in Elastic Cloud you can link Serverless projects and search or analyze data across them from one project (e.g. Observability linked to Security). Shown as tech preview in the Elastic UI. Either wire correlation with A2A via MCP / Agent Builder + workflows (explicit APIs, agents, cases) or lean on CPS when the priority is unified discovery across linked projects—often both make sense for different personas.
From the cloud-path lab
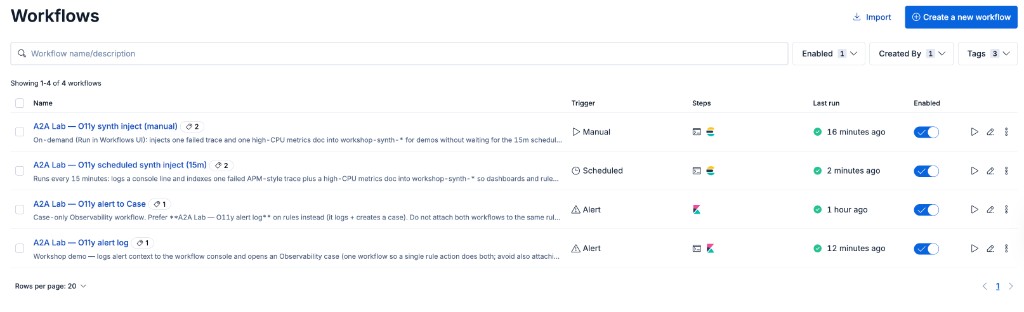
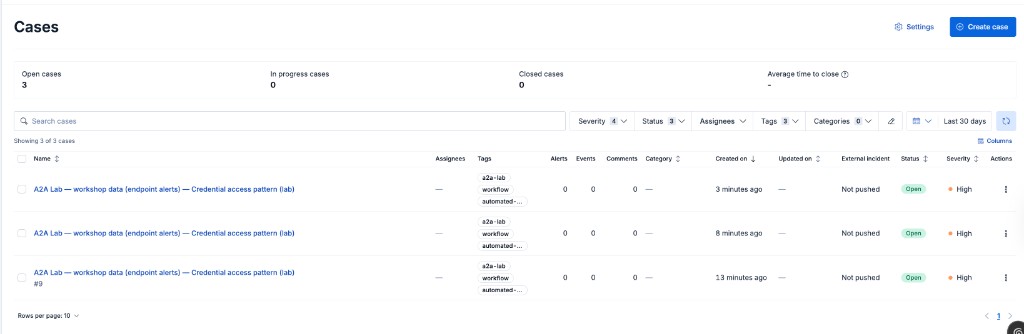
Kibana Workflows and Cases
elastic-agent-builder-a2a-cloud-path pushes workshop workflows to both Kibanas: manual synth inject (Run on demand), scheduled 15m injectors (disabled in YAML until you enable the toggle), and alert workflows that log, call the peer project via HTTP converse, then open a Case with drill text plus the model reply.
Value for sellers & customers
Faster decisions, clearer ROI, a path to response
- Shrink MTTR — fewer round-trips between siloed tools and experts.
- Executive-ready narrative — “attack signal” plus “customer-visible pain” in one view.
- Automation without blind spots — trigger Slack, ticketing, or runbooks with context, not guesswork.
Positioning line: Detect attacks with application impact—not instead of it.
AE training: AI prompt library → — copy-ready prompts for Claude / ChatGPT
Hands-on
Workshop: two serverless projects, one correlation story
The cloud-path scripts provision two Serverless projects, seed workshop-synth-* data, create Agent Builder agents, and PUT the workflow YAML shown on slide 4.
The Instruqt track elastic-a2a-serverless-agent-builder teaches the same A2A story in-browser: Serverless Observability and Serverless Security each get a lab tab, both reverse-proxied through the es3-api lab host (nginx on 8080 / 8081) after learners paste their Cloud Kibana URLs into .env.
- Instruqt — facilitator-led UI + checks; source in
elastic-agent-builder-a2a-workshop/. - BYO Elastic — use
elastic-agent-builder-a2a-cloud-pathand Agent Skills when you are not in a sandbox.
Lab automation (workflows + keys): elastic-agent-builder-a2a-cloud-path →
AE training: AI prompt library → — personas, objections, emails, discovery
Use Next / Prev below, dot buttons, or ← → / Space.